参考:
https://blog.csdn.net/u013028621/article/details/116271537
https://blog.csdn.net/nanyou519/article/details/104953960
http://www.javashuo.com/article/p-svltvgwh-rx.html
上文:http://www.gaohaiyan.com/4047.html
这里还是只看 system/core/rootdir/init.rc
当LoadBootScripts解析完后,ActionManager就开始启动各个指令。
下面代码明确的触发了3个指令:early-init、init、late-init:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 |
int SecondStageMain(int argc, char** argv) { // .... ActionManager& am = ActionManager::GetInstance(); ServiceList& sm = ServiceList::GetInstance(); // .... LoadBootScripts(am, sm); // .... am.QueueEventTrigger("early-init"); //【--- 1 -->】 // .... am.QueueEventTrigger("init"); //【--- 2 -->】 // .... am.QueueEventTrigger("late-init"); //【--- 3 -->】 // .... while (true) { // .... if ( !( prop_waiter_state.MightBeWaiting() || Service::is_exec_service_running() ) ) { am.ExecuteOneCommand(); } // .... } return 0; } |
1.early-init
这里是为Android做一些初始化操作,创建一些属性文件、目录、设定目录权限、启动服务等。后面的2个section,还会根据手机处理器位数启动特定服务。
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 |
# 约15行 # Cgroups are mounted right before early-init using list from /etc/cgroups.json on early-init write /proc/sys/kernel/sysrq 0 write /proc/sys/kernel/modprobe \n restorecon /adb_keys restorecon /postinstall mkdir /acct/uid chown root system /dev/memcg/memory.pressure_level chmod 0040 /dev/memcg/memory.pressure_level mkdir /dev/memcg/apps/ 0755 system system mkdir /dev/memcg/system 0550 system system mkdir /dev/net 0755 root root symlink ../tun /dev/net/tun setrlimit nice 40 40 setrlimit nofile 32768 32768 mkdir /linkerconfig/bootstrap 0755 mkdir /linkerconfig/default 0755 write /sys/module/dm_verity/parameters/prefetch_cluster 0 exec -- /system/bin/linkerconfig --target /linkerconfig/bootstrap chmod 644 /linkerconfig/bootstrap/ld.config.txt copy /linkerconfig/bootstrap/ld.config.txt /linkerconfig/default/ld.config.txt chmod 644 /linkerconfig/default/ld.config.txt mount none /linkerconfig/bootstrap /linkerconfig bind rec start ueventd exec_start apexd-bootstrap update_linker_config mkdir /dev/boringssl 0755 root root mkdir /dev/boringssl/selftest 0755 root root mount tracefs tracefs /sys/kernel/tracing # Run boringssl self test for each ABI so that later processes can skip it. http://b/139348610 on early-init && property:ro.product.cpu.abilist32=* exec_start boringssl_self_test32 on early-init && property:ro.product.cpu.abilist64=* exec_start boringssl_self_test64 |
2.init
同样是创建一些属性文件、目录、设定目录权限、启动服务等。后面的section中property:ro.debuggable=1指如果开启了调试模式,还会启动console服务。
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 115 116 117 118 119 120 121 122 123 124 125 126 127 128 129 130 131 132 133 134 135 136 137 138 139 140 141 142 143 144 145 146 147 148 149 150 151 152 153 154 155 156 157 158 159 160 161 162 163 164 165 166 167 168 169 170 171 172 173 174 175 176 177 178 179 180 181 182 183 184 185 186 187 188 189 190 191 |
# 约114行 on init sysclktz 0 copy /proc/cmdline /dev/urandom copy /system/etc/prop.default /dev/urandom symlink /proc/self/fd/0 /dev/stdin symlink /proc/self/fd/1 /dev/stdout symlink /proc/self/fd/2 /dev/stderr mkdir /dev/stune/foreground mkdir /dev/stune/background mkdir /dev/stune/top-app mkdir /dev/stune/rt chown system system /dev/stune chown system system /dev/stune/foreground chown system system /dev/stune/background chown system system /dev/stune/top-app chown system system /dev/stune/rt chown system system /dev/stune/tasks chown system system /dev/stune/foreground/tasks chown system system /dev/stune/background/tasks chown system system /dev/stune/top-app/tasks chown system system /dev/stune/rt/tasks chmod 0664 /dev/stune/tasks chmod 0664 /dev/stune/foreground/tasks chmod 0664 /dev/stune/background/tasks chmod 0664 /dev/stune/top-app/tasks chmod 0664 /dev/stune/rt/tasks mkdir /dev/stune/nnapi-hal chown system system /dev/stune/nnapi-hal chown system system /dev/stune/nnapi-hal/tasks chmod 0664 /dev/stune/nnapi-hal/tasks write /dev/stune/nnapi-hal/schedtune.boost 1 write /dev/stune/nnapi-hal/schedtune.prefer_idle 1 mkdir /dev/blkio/background chown system system /dev/blkio chown system system /dev/blkio/background chown system system /dev/blkio/tasks chown system system /dev/blkio/background/tasks chmod 0664 /dev/blkio/tasks chmod 0664 /dev/blkio/background/tasks write /dev/blkio/blkio.weight 1000 write /dev/blkio/background/blkio.weight 200 write /dev/blkio/blkio.group_idle 0 write /dev/blkio/background/blkio.group_idle 0 restorecon_recursive /mnt mount configfs none /config nodev noexec nosuid chmod 0770 /config/sdcardfs chown system package_info /config/sdcardfs mkdir /dev/binderfs mount binder binder /dev/binderfs stats=global chmod 0755 /dev/binderfs mount fusectl none /sys/fs/fuse/connections symlink /dev/binderfs/binder /dev/binder symlink /dev/binderfs/hwbinder /dev/hwbinder symlink /dev/binderfs/vndbinder /dev/vndbinder chmod 0666 /dev/binderfs/hwbinder chmod 0666 /dev/binderfs/binder chmod 0666 /dev/binderfs/vndbinder mkdir /mnt/secure 0700 root root mkdir /mnt/secure/asec 0700 root root mkdir /mnt/asec 0755 root system mkdir /mnt/obb 0755 root system mkdir /mnt/media_rw 0750 root external_storage mkdir /mnt/user 0755 root root mkdir /mnt/user/0 0755 root root mkdir /mnt/user/0/self 0755 root root mkdir /mnt/user/0/emulated 0755 root root mkdir /mnt/user/0/emulated/0 0755 root root mkdir /mnt/pass_through 0700 root root mkdir /mnt/pass_through/0 0710 root media_rw mkdir /mnt/pass_through/0/self 0710 root media_rw mkdir /mnt/pass_through/0/emulated 0710 root media_rw mkdir /mnt/pass_through/0/emulated/0 0710 root media_rw mkdir /mnt/expand 0771 system system mkdir /mnt/appfuse 0711 root root mkdir /mnt/runtime 0700 root root mkdir /mnt/runtime/default 0755 root root mkdir /mnt/runtime/default/self 0755 root root mkdir /mnt/runtime/read 0755 root root mkdir /mnt/runtime/read/self 0755 root root mkdir /mnt/runtime/write 0755 root root mkdir /mnt/runtime/write/self 0755 root root mkdir /mnt/runtime/full 0755 root root mkdir /mnt/runtime/full/self 0755 root root symlink /storage/self/primary /mnt/sdcard symlink /mnt/user/0/primary /mnt/runtime/default/self/primary write /proc/sys/kernel/panic_on_oops 1 write /proc/sys/kernel/hung_task_timeout_secs 0 write /proc/cpu/alignment 4 write /proc/sys/kernel/sched_tunable_scaling 0 write /proc/sys/kernel/sched_latency_ns 10000000 write /proc/sys/kernel/sched_wakeup_granularity_ns 2000000 write /proc/sys/kernel/sched_child_runs_first 0 write /proc/sys/kernel/randomize_va_space 2 write /proc/sys/vm/mmap_min_addr 32768 write /proc/sys/net/ipv4/ping_group_range "0 2147483647" write /proc/sys/net/unix/max_dgram_qlen 600 write /proc/sys/kernel/sched_rt_runtime_us 950000 write /proc/sys/kernel/sched_rt_period_us 1000000 write /proc/sys/net/core/rmem_max 262144 write /proc/sys/net/core/wmem_max 262144 write /proc/sys/net/ipv4/fwmark_reflect 1 write /proc/sys/net/ipv6/fwmark_reflect 1 write /proc/sys/net/ipv4/tcp_fwmark_accept 1 write /proc/sys/net/ipv4/conf/all/accept_redirects 0 write /proc/sys/net/ipv6/conf/all/accept_redirects 0 chmod 0400 /proc/net/fib_trie chown system system /dev/cpuctl chown system system /dev/cpuctl/tasks chmod 0666 /dev/cpuctl/tasks write /dev/cpuctl/cpu.rt_period_us 1000000 write /dev/cpuctl/cpu.rt_runtime_us 950000 mkdir /dev/cpuset/foreground copy /dev/cpuset/cpus /dev/cpuset/foreground/cpus copy /dev/cpuset/mems /dev/cpuset/foreground/mems mkdir /dev/cpuset/background copy /dev/cpuset/cpus /dev/cpuset/background/cpus copy /dev/cpuset/mems /dev/cpuset/background/mems mkdir /dev/cpuset/system-background copy /dev/cpuset/cpus /dev/cpuset/system-background/cpus copy /dev/cpuset/mems /dev/cpuset/system-background/mems mkdir /dev/cpuset/restricted copy /dev/cpuset/cpus /dev/cpuset/restricted/cpus copy /dev/cpuset/mems /dev/cpuset/restricted/mems mkdir /dev/cpuset/top-app copy /dev/cpuset/cpus /dev/cpuset/top-app/cpus copy /dev/cpuset/mems /dev/cpuset/top-app/mems chown system system /dev/cpuset chown system system /dev/cpuset/foreground chown system system /dev/cpuset/background chown system system /dev/cpuset/system-background chown system system /dev/cpuset/top-app chown system system /dev/cpuset/restricted chown system system /dev/cpuset/tasks chown system system /dev/cpuset/foreground/tasks chown system system /dev/cpuset/background/tasks chown system system /dev/cpuset/system-background/tasks chown system system /dev/cpuset/top-app/tasks chown system system /dev/cpuset/restricted/tasks chmod 0775 /dev/cpuset/system-background chmod 0664 /dev/cpuset/foreground/tasks chmod 0664 /dev/cpuset/background/tasks chmod 0664 /dev/cpuset/system-background/tasks chmod 0664 /dev/cpuset/top-app/tasks chmod 0664 /dev/cpuset/restricted/tasks chmod 0664 /dev/cpuset/tasks chown system system /proc/pressure/memory chmod 0664 /proc/pressure/memory chown root net_bw_acct /proc/net/xt_qtaguid/ctrl chown root net_bw_stats /proc/net/xt_qtaguid/stats chmod 0644 /dev/xt_qtaguid mount bpf bpf /sys/fs/bpf nodev noexec nosuid mkdir /dev/fscklogs 0770 root system mount pstore pstore /sys/fs/pstore nodev noexec nosuid chown system log /sys/fs/pstore chmod 0550 /sys/fs/pstore chown system log /sys/fs/pstore/console-ramoops chmod 0440 /sys/fs/pstore/console-ramoops chown system log /sys/fs/pstore/console-ramoops-0 chmod 0440 /sys/fs/pstore/console-ramoops-0 chown system log /sys/fs/pstore/pmsg-ramoops-0 chmod 0440 /sys/fs/pstore/pmsg-ramoops-0 write /proc/sys/abi/swp 1 symlink /proc/self/fd /dev/fd export DOWNLOAD_CACHE /data/cache write /sys/class/leds/vibrator/trigger "transient" write /dev/cpu_variant:${ro.bionic.arch} ${ro.bionic.cpu_variant} chmod 0444 /dev/cpu_variant:${ro.bionic.arch} write /dev/cpu_variant:${ro.bionic.2nd_arch} ${ro.bionic.2nd_cpu_variant} chmod 0444 /dev/cpu_variant:${ro.bionic.2nd_arch} chown system system /sys/power/state chown system system /sys/power/wakeup_count chmod 0660 /sys/power/state chown radio wakelock /sys/power/wake_lock chown radio wakelock /sys/power/wake_unlock chmod 0660 /sys/power/wake_lock chmod 0660 /sys/power/wake_unlock start logd chown root system /sys/module/lowmemorykiller/parameters/adj chmod 0664 /sys/module/lowmemorykiller/parameters/adj chown root system /sys/module/lowmemorykiller/parameters/minfree chmod 0664 /sys/module/lowmemorykiller/parameters/minfree start lmkd start servicemanager start hwservicemanager start vndservicemanager # 约1053行 on init && property:ro.debuggable=1 start console |
3.late-init
这个厉害了,启动了一串其它Action。关注“trigger zygote-start”一项触发新的Action。
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 |
# 约415行 # Mount filesystems and start core system services. on late-init trigger early-fs trigger fs trigger post-fs trigger late-fs trigger post-fs-data trigger load_persist_props_action trigger load_bpf_programs trigger zygote-start //【--- 4 -->】 trigger firmware_mounts_complete trigger early-boot trigger boot |
4.zygote-start
名称为zygote-start的action有6项。前3个用于挂载特定目录,是并列关系,对应“persist.sys.fuse”的不同情况;后3个用于下一步启动zygote进程,也是并列关系,对应“ro.crypto.state”的不同情况。看以“start”指令的Command,“start zygote”表示启动zygote服务(进程)。
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 |
# 约797行 # Switch between sdcardfs and FUSE depending on persist property # TODO: Move this to ro property before launch because FDE devices # interact with persistent properties differently during boot on zygote-start && property:persist.sys.fuse=true # Mount default storage into root namespace mount none /mnt/user/0 /storage bind rec mount none none /storage slave rec on zygote-start && property:persist.sys.fuse=false # Mount default storage into root namespace mount none /mnt/runtime/default /storage bind rec mount none none /storage slave rec on zygote-start && property:persist.sys.fuse="" # Mount default storage into root namespace mount none /mnt/runtime/default /storage bind rec mount none none /storage slave rec # It is recommended to put unnecessary data/ initialization from post-fs-data # to start-zygote in device's init.rc to unblock zygote start. on zygote-start && property:ro.crypto.state=unencrypted # A/B update verifier that marks a successful boot. exec_start update_verifier_nonencrypted start statsd start netd start zygote //【--- 5.1 -->】 start zygote_secondary //【--- 5.2 -->】 on zygote-start && property:ro.crypto.state=unsupported # A/B update verifier that marks a successful boot. exec_start update_verifier_nonencrypted start statsd start netd start zygote start zygote_secondary on zygote-start && property:ro.crypto.state=encrypted && property:ro.crypto.type=file # A/B update verifier that marks a successful boot. exec_start update_verifier_nonencrypted start statsd start netd start zygote start zygote_secondary |
5.service zygote
Android 5.0以后,Android开始支持64位编译。
init.rc头部引入了带有“关键字”的其它rc:“import /system/etc/init/hw/init.${ro.zygote}.rc”,但是在aosp源码的这个目录下并没有相关文件。和init.rc同目录下却有这么几个:
system/core/rootdir/init.zygote32.rc --------- > 对应32位处理器。没有“service zygote_secondary”
system/core/rootdir/init.zygote32_64.rc ---- > 32位为主,64位为辅(如果product的cpu是32位,顺便支持64位app?)。有
system/core/rootdir/init.zygote64.rc --------- > 64位处理器,没有“service zygote_secondary”
system/core/rootdir/init.zygote64_32.rc ---- > 64位为主,32位为辅。有
以MiNote3+lineageos18.1为例,对应文件的目录:
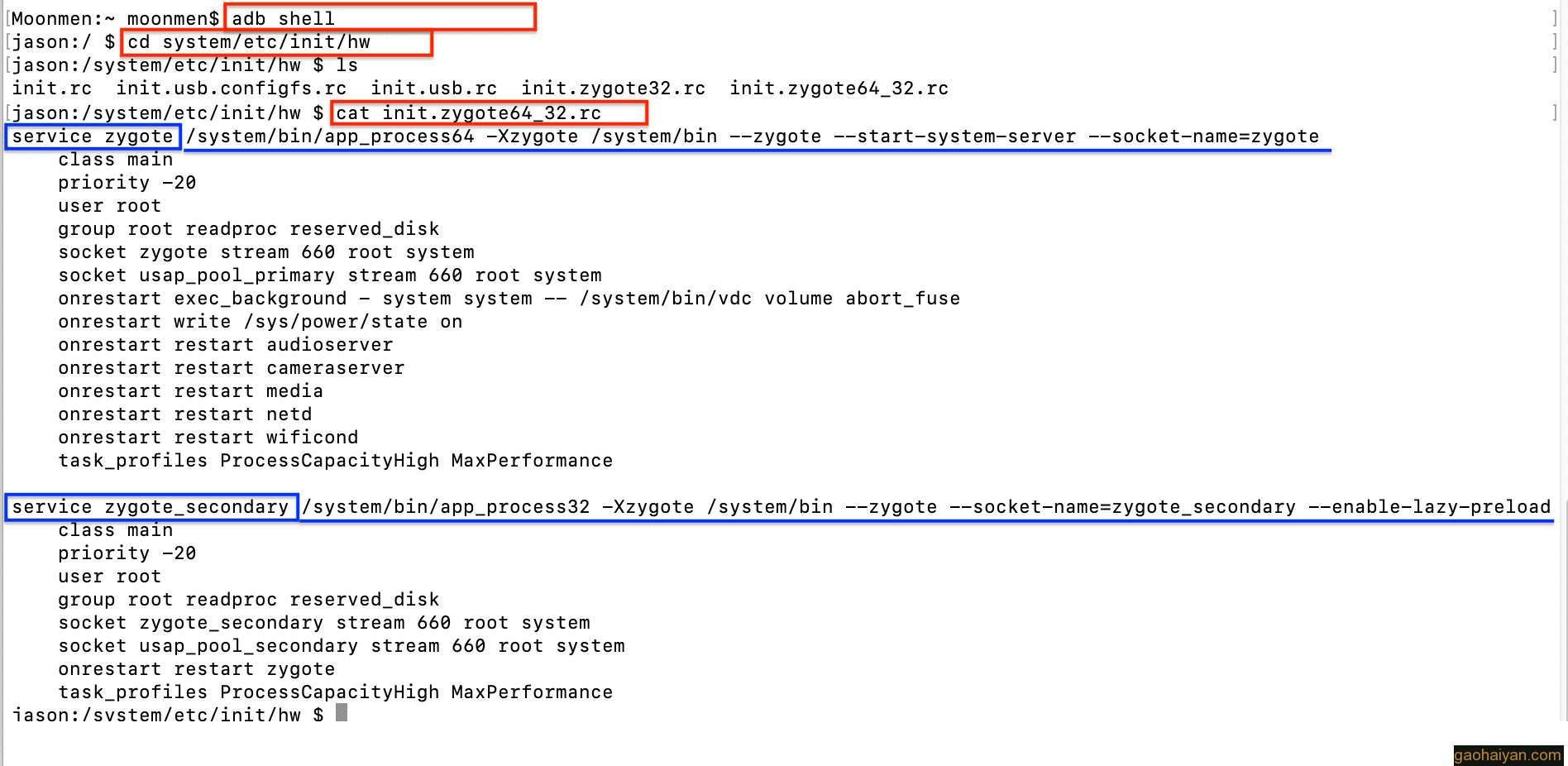
看一下init.zygote64_32.rc的内容:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 |
service zygote /system/bin/app_process64 -Xzygote /system/bin --zygote --start-system-server --socket-name=zygote class main priority -20 user root group root readproc reserved_disk socket zygote stream 660 root system socket usap_pool_primary stream 660 root system onrestart exec_background - system system -- /system/bin/vdc volume abort_fuse onrestart write /sys/power/state on onrestart restart audioserver onrestart restart cameraserver onrestart restart media onrestart restart netd onrestart restart wificond task_profiles ProcessCapacityHigh MaxPerformance service zygote_secondary /system/bin/app_process32 -Xzygote /system/bin --zygote --socket-name=zygote_secondary --enable-lazy-preload class main priority -20 user root group root readproc reserved_disk socket zygote_secondary stream 660 root system socket usap_pool_secondary stream 660 root system onrestart restart zygote task_profiles ProcessCapacityHigh MaxPerformance |
可见,zygote服务的启动文件是 /system/bin/app_process64 。
- end
本文由崔维友 威格灵 cuiweiyou vigiles cuiweiyou 原创,转载请注明出处:http://www.gaohaiyan.com/4062.html
承接App定制、企业web站点、办公系统软件 设计开发,外包项目,毕设